Microsoft 365 comes equipped with numerous security features that are up and running as soon as you sign in. Security experts are continuously monitoring data traffic to detect suspicious activity. They are testing defenses by having an internal team try to hack into the system against a team trying to defend it called Red VS Blue exercises. This probes Microsoft’s service for vulnerabilities to track the latest emerging threats. The Red Team (the hackers) use creative methods and the latest technologies to keep the Microsoft 365 Security team on their toes. All these security features and much more are why getting Microsoft 365 is a huge step up for your security needs.
While many of these features come automatically turned on here are eight steps you can take to increase your company’s security that are completely free.
Check Your Security Score
This score will give you a great understanding of where your company currently stands. Based on your score, Microsoft will provide you with specific recommendations on how to improve your security. This will help you to detect any vulnerabilities and where you should focus on improving.
Set Up Multi-Factor Authentication
The easiest and most effective way to protect against a stolen password or compromised credentials is Multi-Factor Authentication. When someone logs into your account a confirmation will get sent to your smartphone to ensure you are trying to sign in. If you don’t confirm the login the account will stay signed out even if the correct password is being used. This prevents anyone signing into your account without your approval. Multi-Factor Authentication is easy to set up and extremely effective. A must have for any business.

An Educated Team
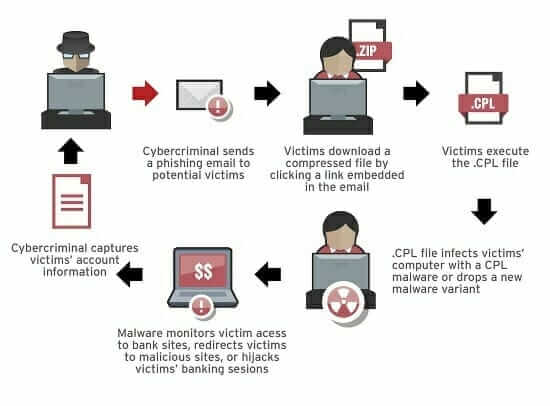
Keeping your team up to date on all company security protocol is essential to mitigating human error. Many security attacks rely on tricking an employee into giving up company data without realizing what they’re doing. Reviewing common attack scenarios and what to look out for can be a key ingredient in keeping your data secure. We recommend creating a document for all users outlining how to be an essential part of your network security.
Build in Device Management Tools
Remote access to corporate data and apps is essential to many businesses. Microsoft 365 makes this easy by providing options to access email, documents, and corporate data from your personal devices. To ensure this data stays secure add a PIN that is required on all devices connected to your network. Device management tools also allow you to wipe all corporate data from devices if they get lost or stolen.
Create a Separate Account for Performing Administrative Tasks
IT managers are a prime target for hackers. If you are using your main Microsoft 365 account to make network changes the keys to all accounts can be vulnerable. The administrative accounts you use to administer your Microsoft 365 environment come equipped with elevated privileges which is why admin accounts should only be used for administration. By creating a separate account for non-administrative use, you can minimize what a potential hacker can gain access too. It’s also a great idea to close all unrelated browser sessions and apps (including personal email accounts) before using your admin account. In addition, you should always log out of your browser sessions when finished. By pairing these tips with MFA you’re setting yourself and your company up for a successful security environment.
Block Malicious Malware in Mail
Everyday millions of new pieces of malware are detected. Malware is commonly hidden in email attachment. By blocking attachments with file types commonly used for malware you can increase your email protection. Common types of malware include viruses, spyware, and ransomware. Viruses infect programs and data. They spread through your computer looking for programs to infect. Spyware will gather your private information such as sign in information and send it back to the hacker. Ransomware encrypts data and requires payment for the hacker to decrypt it. By activating the “Common Attachment Types” filter you can prevent many of these attacks. Learn the steps here.
Store Files in OneDrive for Business
Always keep copies of your files stored in OneDrive for Business. This allows you to leverage the security of the cloud to protect your files. Not only will they be easier for you to access remotely but they will also be safer. Ransomware attacks are becoming increasingly common and can jeopardize a company. By storing your files remotely, you can simply wipe ransomware from your computer and re-download your files if your computer becomes infected. This can downgrade such attacks from a company ending tragedy to simply an inconvenience.
Stop Auto-Forwarding Your Email
If a hacker gains access to a user’s mailbox they can create a rule to automatically forward your emails to their inbox. This can happen without the user’s knowledge and can be destructive. If they don’t gather company information from the emails themselves, they can learn how you speak, sign off, and who you communicate with via email. This provides the hackers with all the information they need to create phishing emails to extract data from your coworkers.
Contact 360 Visibility to speak with our Cloud Cyber Security team. We will work with you so that your technology and staff adopt security best practices, ensuring your business is protected from potential cloud security threats.



