What is Multi-Factor Authentication?
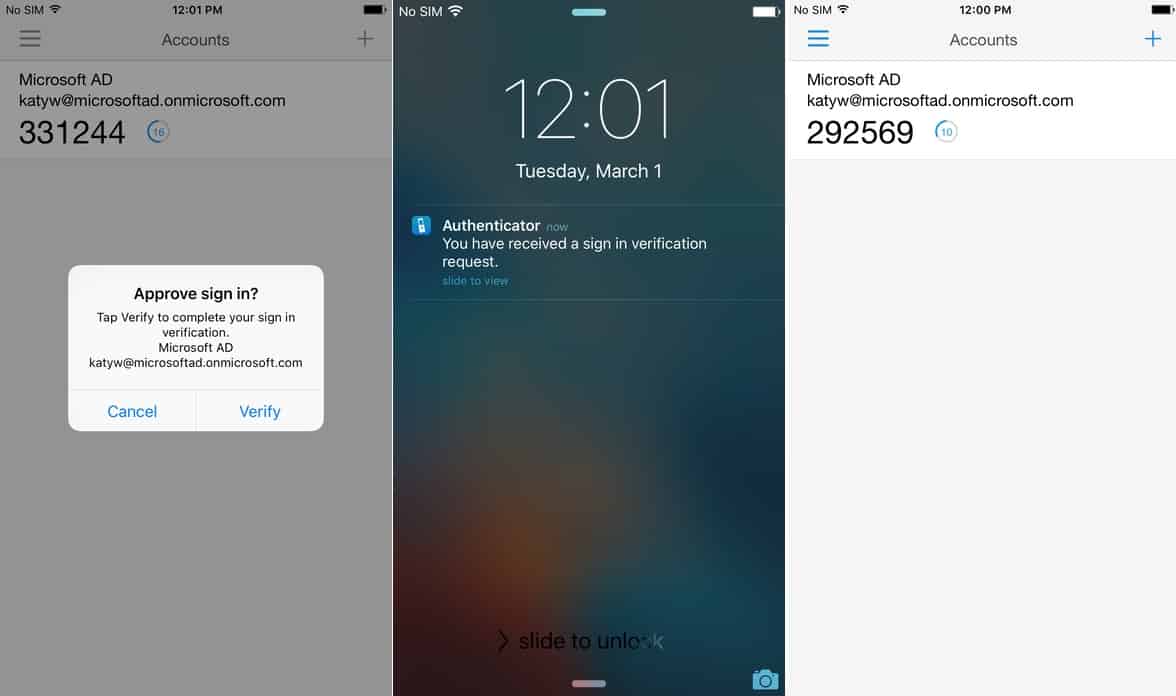
Multi-Factor Authentication (MFA) is a protective measure put in place to verify a user’s identity beyond entering a username and password. MFA also requires the user to provide an additional credential via their smartphone. Once a username and password has been entered a notice will go to their smartphone which requires them to confirm they are trying to log in.
MFA typically uses one of three types of authentication methods:
- Possession – This method of authentication relies on messaging the account holder’s smartphone and the user simply pressing accept as the assumption is that only the user would be in possession of their phone.
- Knowledge – This method requires additional information that only the user would know. This is in the form of a pin or a skill testing question to confirm identity.
- Inheritance – This authentication method requires the user to prove their identity through biometrics. This could require a finger print scan, voice recognition, or a facial recognition.
This is a quick and easy security measure to provide enhanced identity access management protection. According to the 2017 Verizon Data Breach Investigative Report “81% of data breaches involved weak or stolen credentials.” Sophisticated attacks can result in the users account information being posted and sold on the dark web.
By enabling MFA you can prevent some of the most common and successful cyberattacks.
Phishing
The attacker will email or call a list of contacts with a compelling message and a call to action that requires the recipient to enter private information. This individual could be disguised as a well-known business asking you to verify transactions. They will then provide you a link to a fake website, that is disguised to look like the real one, asking you to enter your user name and password. Spear Phishing is similar where the attacker targets a smaller group of individuals providing personal details to make the email more believable. The email will be tailored to the individual it is sent to typically including their name and a recent activity or event to make it more believable.
Man-In-The-Middle Attacks
This type of attack occurs when the hacker inserts themselves in between a communication the parties believe is private. For this to work it is key that the victims believe they are speaking directly to each other and the hacker isn’t detected. This can be between users or a user and an app or two users. The attacker will intercept messages between parties and send their own to gather private information.
Brute Force
The hacker will use a program that generates possible password and username combinations until one works. In a reverse brute-force attack, attackers try common passwords with many different usernames on a variety of sites until they gain access to an account.
Keyloggers
The attacker installs a software onto the user’s computer via a virus that tracks (or logs) the keystrokes on the user’s computer. This includes the websites the user visits, usernames, and passwords. Depending on what they do while the software is on their computer this could also include answers to security questions.
Credential Stuffing
Once the attacker has found a successful username and password combination, they try using that information on a variety of websites banking on the fact that the user has the same username and password on a variety of websites and apps.
Related Article: Microsoft Cloud App Security (MCAS)
How Multi-Factor Authentication Can Protect Against Common Cyber Attacks
The forms of cyberattacks listed above rely on the attacker finding a username and password combination that works to enter an account. By requiring additional information/credentials from the user it makes it much more difficult to have your account hacked. Typically, MFA gathers its additional data from the user’s smartphone which is in their possession. This can be in the form of an authentication code sent to your phone, fingerprint scan, face scan, or security question. All of which are much more difficult to acquire than a username and password. This will also notify you if someone is trying to gain access to your account.
How to Enable Multi-Factor Authentication
Azure Multi-Factor Authentication is provided with the following offerings:
Azure Active Directory Premium or Microsoft 365 Business – Full featured use of Azure Multi-Factor Authentication using Conditional Access policies to require multi-factor authentication.
Azure AD Free, Azure AD Basic, or standalone Office 365 licenses – Use pre-created Conditional Access baseline protection policies to require multi-factor authentication for your users and administrators.
Azure Active Directory Global Administrators – A subset of Azure Multi-Factor Authentication capabilities available to protect global administrator accounts.
Enable Conditional Access Policies
Conditional access can be enabled by a company to ensure security is maintained. By implementing a set of conditions that require MFA an organization can maintain control of their information and who is accessing it. Additional credentials could be requested if there is a sign-in attempt from an unfamiliar location, sign-in from IP address that is unknown or has had suspicious activity, sign-in from atypical devices, or infected devices. This uses MFA in a specific set of circumstances as opposed to during every log in attempt.
Start Using Multi-Factor Authentication
Azure Multi-Factor Authentication is an easy and effective way to protect a business from malicious attacks. 360 Visibility can implement MFA to help keep your information secure. We are a Tier 1 Microsoft Cloud Solutions Provider and Managed IT Service Provider specializing in Cloud Security, Office 365, and Microsoft Dynamics. Start using MFA in your business to See Clearly and Act Faster while having peace of mind that your business is safe.



